Australia is firmly in the sights of North Korea’s aggressive thousands-strong army of agents posing as remote IT workers.
The first clue that the neat, carefully spoken man on the Zoom screen was not merely a prospective employee for an Australian tech company but a secret agent for the North Korean regime was his struggle to describe where he lived in New York.
The man claiming to be Aaron Pierson calmly described how his IT prowess could help the Australian start-up flourish.
But he hesitated when quizzed about which of New York’s famous five boroughs he claimed to have spent three years in while at university.
“New York City” was all he could initially muster. When pushed, he said he had lived on the “west coast, um, I mean west part of New York”.
He was equally tongue-tied when asked about major landmarks surrounding his supposed current address in California’s Silicon Valley.
For a proud American hoping for a start in Australia’s burgeoning artificial intelligence sector, “Aaron” was also in the dark about US professional sports.
He preferred to play soccer with friends, Aaron said nervously.
Nerves turned to nastiness when asked why he looked nothing like the profile picture used by the real Aaron Pierson, or at least the Pierson who had spent months applying for IT jobs at large multinational firms using the same résumé as the man now on the Zoom call.

That earlier version of Pierson was a black American detected by Five Eyes security agencies and Australian cyber firm DTEX during efforts to track an extraordinary operation by Kim Jong-un’s security apparatus infiltrating Western companies using an army of undercover operatives posing as stay-at-home and remote IT workers.
The Aaron Pierson now on the screen was Asian and apparently no longer that job hungry.
“Hey, sorry, I’m not too interested any more,” he said when pushed on this discrepancy over appearance.
His annoyance and suspicion was justified because “Aaron” had stumbled into a trap. The job didn’t exist and he was not the only participant on the Zoom call pretending to be somebody else.
The man quizzing him online was one of this story’s authors, posing as a cyber and AI industry recruiter.
The subterfuge was an attempt to catch the North Korean regime in the act at a time when Australia’s spy chief, Mike Burgess, warns this country is firmly in the sights of a thousands-strong North Korean army of agents posing as remote IT workers.

“This is a very real concern,” said Burgess, in an exclusive interview with this masthead and 60 Minutes, of an operation the United Nations believes nets North Korea $800 million a year.
Burgess’ agency, ASIO, has identified undercover operatives targeting Australian firms hoping to funnel salaries back to fund Kim Jong-un’s weapons programs.
The ingenious operation works partly because Australian firms have failed to counter the emerging problem, which has also potentially exposed these companies and the wider community to risk.
“For me, that’s why I’m prepared to talk about this as [ASIO] director-general. That’s the same vulnerability that could be used for espionage, foreign interference and the preparation for sabotage, or just purely, ‘I’m defrauding you to make some money to pay my government’,” Burgess said.
“The cost is real-world impact on our people and our economy, and that’s why people and companies should care.”
Law enforcement sources confirmed that major banks, including NAB, have been infiltrated, while the Australian Federal Police’s cyber threat teams are assessing intelligence that North Korean agents are already onshore, including a Melbourne University alumnus-turned suspected regime intermediary.

Mohan Koo, the founder of cybersecurity company DTEX, said Australian firms were already compromised and the situation might worsen.
“I would say, dozens right now is a pretty safe bet, but this can quite quickly explode,” he said, pointing to the experience of the United States, where firms have unwittingly hired North Korean agents as remote IT workers for a decade.
Last year, the FBI warned that this North Korean operation was becoming “increasingly malicious” and publicly urged American companies to strengthen their defences. Now, Burgess and Koo offer the same urgent plea to corporate Australia to overhaul its recruitment practices.
“You’ve got people who are pretending to be someone who can do some coding skills or some form of IT discipline and they’re selling themselves online,” Burgess said.
“They may well be interviewed online. Of course, they can use artificial intelligence to change their voice and their face. They get the job, they get given access to a system, and they can actually, for the most part, do work that you need them to do. And, of course, you’ve given access to someone who is North Korean and you can’t trust them.”
Koo said security-lite online recruiting had super-charged the North Korean operation.
“The advent of COVID meant that every company on the planet basically had to hire remote people,” he said.
“Unless you’re actually seeing someone face to face, how do you guarantee that they are who they say they are?”
While Australia is just waking up to the problem, US agencies have already raided and jailed operatives and identified the infiltration of major firms, including Boeing, NBC and Nike.
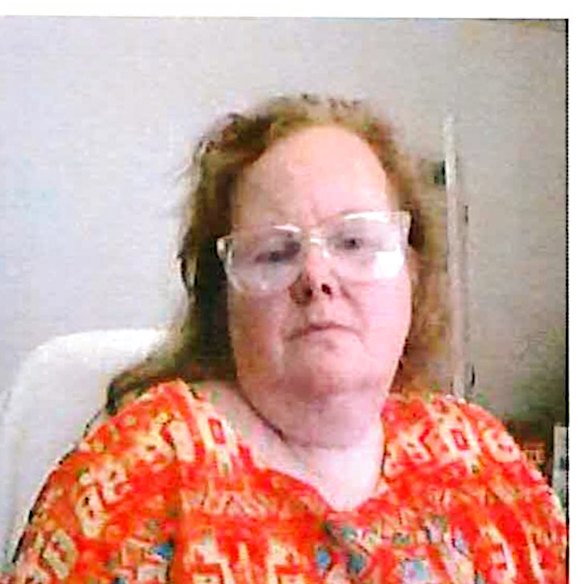
The highest profile case in America involved an Arizonan woman who was recruited online by a North Korean operative.
According to her indictment, Christina Chapman acted as what is known as a “laptop farmer”: a person willing to host and operate the computers that companies send to workers after they are hired online under an alias.
More than 300 American firms posted laptops to Chapman, which she duly plugged in and connected to dozens of North Koreans who had landed jobs.

Chapman was jailed for 8½ years, and the prosecutor in the case, United States Attorney for the District of Columbia Jeanine Pirro, described the Arizonan’s offending not only as prolific but a stark reminder for Australia.
“This ordinary, nondescript woman was able to pretty much funnel $17 million to North Korea,” Pirro said.
“Countries like Australia are fertile ground, where there is no suspicion, where identities can be stolen or faked, and where these foreign actors are looking to make new inroads.”
Pirro said the real lesson from the Chapman case was how supposedly security-conscious global companies such Nike could be so easily duped.

“We had big companies that got caught up in this because they weren’t checking to make sure that the person who was logging on was a person who applied for the job,” Pirro said.
“Most Fortune 500 companies will not admit to that but we had quite a few of them who were willing to do so. And credit and kudos to Nike for saying, ‘You know what? It happened to us and it could happen to you’.”
If anyone is familiar with this reality, it’s DTEX’s lead investigator, Michael Barnhart.
After the 2001 terrorist attacks on the US, Barnhart served as a US intelligence official alongside the military across the Middle East, combating Islamic extremists. Tattooed and propelled by a seemingly relentless nervous energy, Barnhart describes Kim Jong-un’s online operatives as “so opportunistic, so clever”.
“They understand how crime works and they use that crime to further nation state goals,” he said.
In Australia, Barnhart’s DTEX office is in Lot Fourteen, the South Australian government’s cyber, AI and technology innovation hub. It may feel as sleepy as the city hosting it, but Lot Fourteen has had its share of scandal.

A few doors down are the offices of one of the space industry hub firms that previously employed consultant Marina Solugub, an Irish woman accused by ASIO of working for Russian spy services as they sought to penetrate Australia and other allies among the Five Eyes nations.
From DTEX’s secure bunker, Barnhart fights alongside a group of cyber sleuths he has dubbed the “misfits”: a small, informal team of former spooks and ex-law enforcement officials, reformed hackers and digital denizens who scour the internet in pursuit of North Korean agents posing as IT workers.
These agents are outed by their trail of online bread crumbs left as they juggle multiple jobs using multiple identities and digital platforms. For instance, the same North Korean operative might post different résumés online using different names but the same photo.
When a suspected agent is confirmed as a regime operative, the misfits alert the unwitting employer as well as Five Eyes law enforcement and intelligence agencies. The Five Eyes nations are Australia, New Zealand, the UK, Canada and the US.
The North Korean operation’s success relies on its scale, leading to inevitable human mistakes.
In selfies snapped to create a fake social media profile, Barnhart’s team discovered an agent who had photographed himself unaware that three of his North Korean accomplices were visible in the background of one of his pictures.
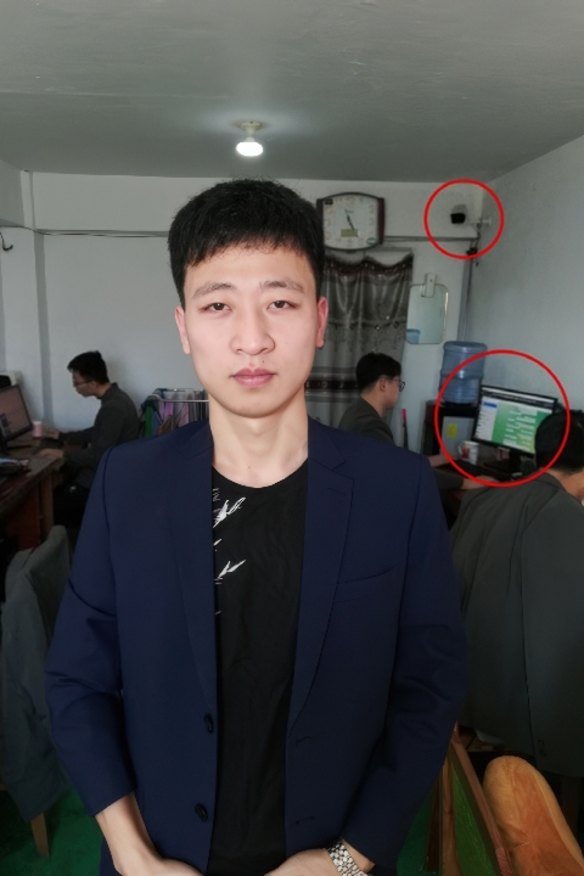
He’s dressed in smart office attire, but his accomplices are wearing the military greens of North Korea’s security apparatus. Closer inspection uncovers CCTV cameras inside the man’s office, revealing it as a likely military facility and suggesting the selfie-taker and his colleagues are being monitored as they apply for and work their jobs for Western companies.
As his focus has turned from the US to Australia, Barnhart’s sleuthing identified a suspected North Korean IT team using the identity of a supposed Queenslander, going by the first name Kaiden.
A further Google search identified an apparently photoshopped water bill connected to a Sydney house, a document presumably used by the North Koreans to create false Australian identities.
A visit to the house found only a rusting ute on an overgrown front lawn and a confused owner named Wayne who had no idea his address was stolen by foreign agents.

Once DTEX, Barnhart or his fellow misfits positively identify a North Korean operative, they are covertly targeted, which includes the contents of their laptops. Suddenly, the spies are being spied upon.
During one such infiltration, DTEX uncovered a spreadsheet in which a mid-level North Korean agent kept a running tally of all the countries his team of IT workers were targeting.
The spreadsheet revealed the agent was running about 40 IT workers across 12 teams and that their targets included Australian firms.
“[The firms] don’t realise they have a hand in an adversarial nation’s weapons program, but this absolutely is the smoking gun saying that they do,” Barnhart said.
The search history of another North Korean agent suggests the group are actively targeting an Australian drone and laser company headquartered in Melbourne.
‘I’m starting to get a little bit jack of people falling for this.’ASIO Director-General Mike Burgess
While defence industries are an obvious target, another Australian sector under assault is the building and engineering design industry.
Koo, from DTEX, said that if Australian firms are, as he suspects, unwittingly outsourcing engineering or building design tasks to North Korea, the corresponding sabotage risks read like a “horror film”.
Sometimes, compromised companies push back, including firms incredulous that their employee of the month is actually a team of 15 North Koreans stationed in a Pyongyang military facility or bunker in a friendly country, such as Russia or China.
“They have 10, 15 different individuals doing the work of that one employee. Sometimes the work is so good that when we catch them out, the employer says, ‘No, you can’t fire that individual. They are my best employee’,” Koo said.
ASIO’s Burgess is clearly frustrated that sections of corporate Australia are not taking the threat seriously.
“I’ve been in this business for a long time now, and I’ve been around cybersecurity for a long time, and to be honest … I’m starting to get a little bit jack of people falling for this,” he said.
“This is very real and it’s just another example of how something that is knowable and foreseeable is not being dealt with effectively.”
The threat facing Australian firms is growing as North Korea’s online army receives continuous training and technical support from China.
Job interviews covertly filmed by DTEX reveals interviewees also increasingly rely on AI to alter their appearance and voice.
North Korea also uses AI to scour the internet for online job advertisements, apply for jobs and then correspond with recruiters.
This appeared to be the case when American IT professional “Aaron Pierson” applied for a new role with the nascent, and fictitious, Australian AI and cyber company that was created in the hope of catching a North Korean in the act.
On paper, Aaron was an attractive candidate, with a New York University computer science degree and claimed stints at Walmart and Bayer.
But the impressive and detailed education and job history on Aaron’s résumé also matched details supplied by job applicants with other companies with different names. Aaron Pierson was also David Ye and David Rose.
Asked to provide details, in the video interview, about his life outside work in California, Aaron’s calm if stilted demeanour slowly crumbled.
He could not even offer up Manhattan or Brooklyn when asked for his favourite New York City location.
The strength of the North Korean operation is Western firms’ insatiable demand for cheaper offshore IT contractors, and its obvious weakness is laid bare with a simple request to attend an in-person induction.
When a meeting is suggested to Aaron to shake his hand, his appetite for the job on offer begins to dissipate.
The journey to Australia is too long, he said.
As questions became more pointed, Aaron becomes terser. The regime’s operatives are prohibited from speaking ill of Kim Jong-un.
When asked what he thinks of North Korea he said: “I’m not sure. I don’t have any idea about that.”
Asked if he had ever heard of Kim Jong-un, Aaron replied: “No. I don’t know … I have no idea.”
When told that recruiting a North Korean could put an Australian employer in breach of sanctions, Aaron deflects.
“Hey, I’m actually not sure why, um, such questions are being asked at this interview,” he said.
Presented with the evidence he is not who he says he is, Aaron ends the call.
Aaron’s inability to summon a credible backstory and the discovery of his multiple personalities invites an underestimation of the threat posed by the thousands of jobseekers working in North Korea’s enterprise.
Companies have already been compromised. If a major bank like the tech-savvy security NAB can employ a North Korean agent (albeit only to discover his infiltration and sack him), then less capable Australian firms are at greater risk.
Burgess believes there is a need for urgent action.
“If they’re on the network, they can learn how your business operates, how your networks operate,” the ASIO head said.
“If you’re a critical business, they could work out how to disrupt that should that ever be needed. They could do that to hold you to ransom at some stage, or they could do that to generate what we call ‘an effect’ in a time of crisis.
“This is a nation state operating as an organised crime gang [capable of pivoting to] espionage … or the preparation for sabotage.
Start the day with a summary of the day’s most important and interesting stories, analysis and insights. Sign up for our Morning Edition newsletter.
Disclaimer : This story is auto aggregated by a computer programme and has not been created or edited by DOWNTHENEWS. Publisher: www.smh.com.au







